How to Protect Data from Identity Theft: A Comprehensive Guide
Introduction
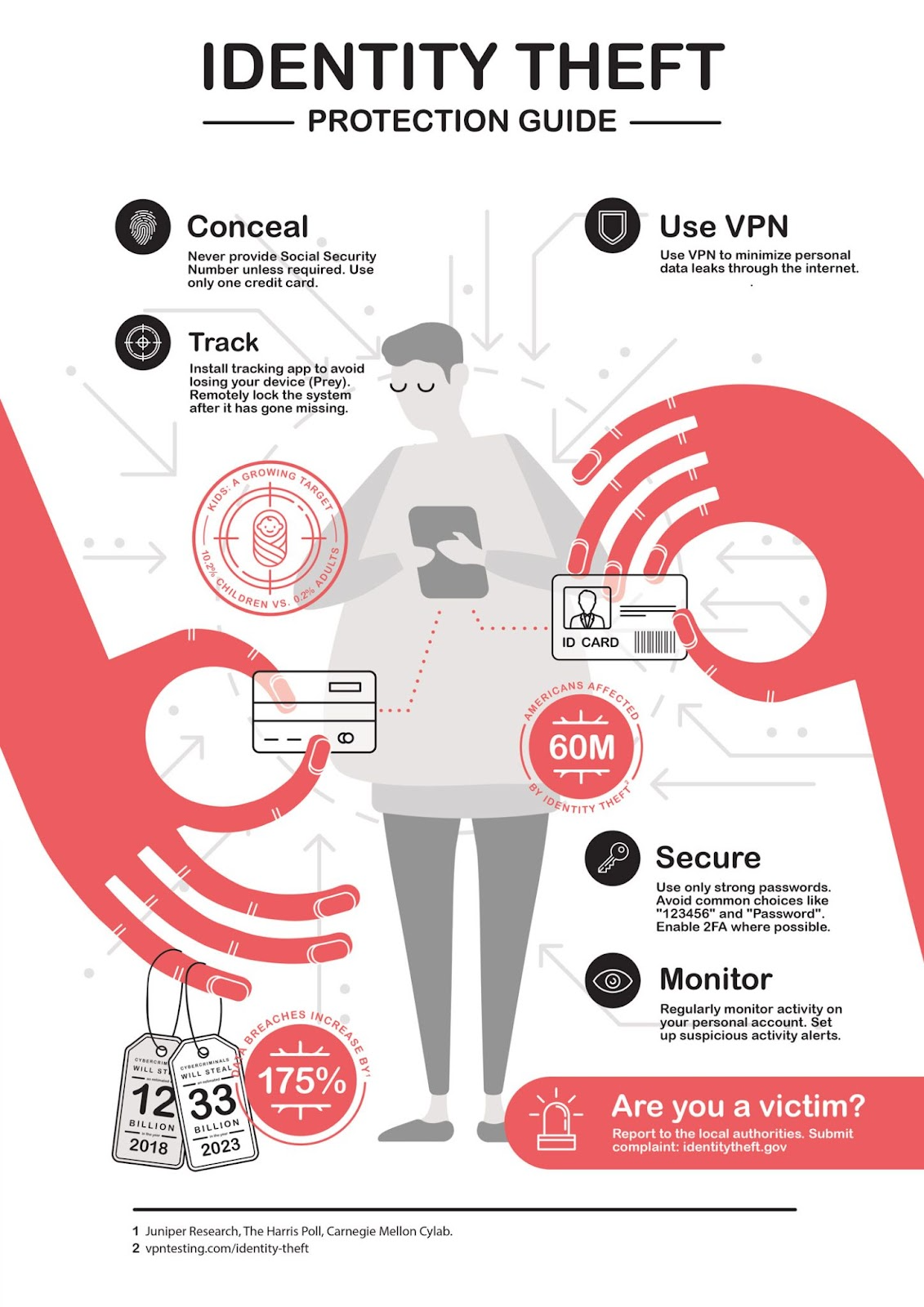
Identity theft is a growing concern in today's digital age. With the increasing frequency of data breaches and cyber attacks, it's essential to take proactive steps to protect your personal information and prevent identity theft. In this article, we will discuss the various ways to protect your data from identity theft and provide you with a comprehensive guide to help you safeguard your identity. Identity theft occurs when an individual uses another person's personal information, such as their name, address, social security number, or credit card number, without their consent. This can lead to financial loss, damaged credit, and a long recovery process. According to the Federal Trade Commission (FTC), identity theft affects over 40 million Americans each year.How to Protect Data from Identity Theft

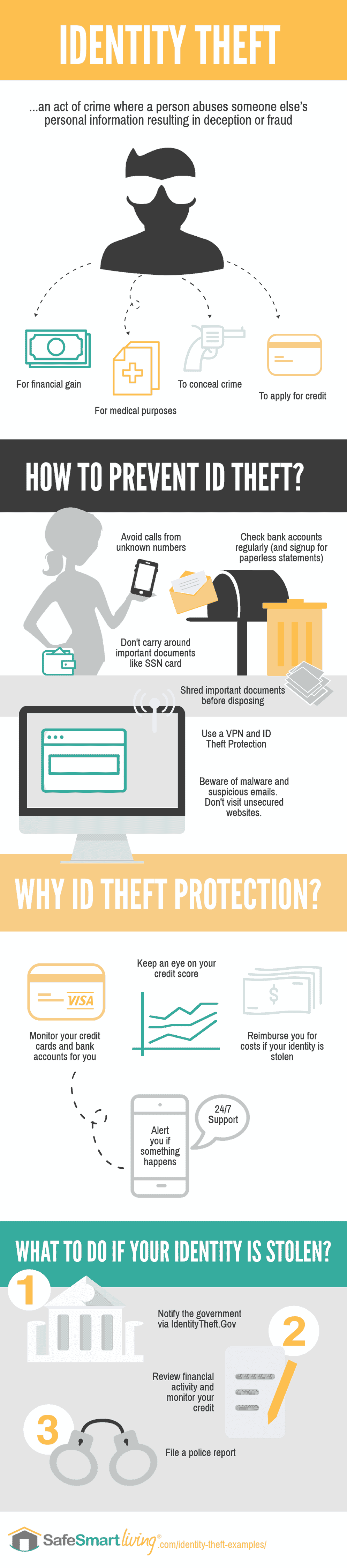
Shredding Sensitive Documents
One of the simplest ways to prevent identity theft is to shred sensitive documents, such as financial statements, tax returns, and credit card applications. This will prevent criminals from accessing your personal information.Using Password Managers

This particular example perfectly highlights why How To Protect Data From Identity Theft is so captivating.
Using a password manager is an effective way to protect your online accounts from hackers. A password manager can generate and store unique, complex passwords for each of your online accounts, ensuring that your personal information remains safe.Enabling Two-Factor Authentication
Two-factor authentication (2FA) is a security measure that requires you to provide a second form of verification, such as a code sent to your phone or a fingerprint, in addition to your password. This makes it much harder for hackers to access your online accounts.Checking Credit Reports

As we can see from the illustration, How To Protect Data From Identity Theft has many fascinating aspects to explore.
Checking your credit report regularly can help you detect any suspicious activity, such as new accounts opened or credit inquiries. You can obtain a free credit report from each of the three major credit reporting agencies annually.



![How to Prevent Identity Theft With 20 Essential Steps [Updated 2026] How to Prevent Identity Theft With 20 Essential Steps [Updated 2026]](https://www.openedr.com/blog/wp-content/uploads/2025/10/id-theft-protection.png)