Unlocking the Power of GHz Router Access Control List: A Comprehensive Guide
In the world of networking, ensuring the security and control of network traffic is crucial. One of the most effective ways to achieve this is by utilizing Access Control Lists (ACLs) on GHz routers. In this article, we will delve into the world of GHz Router Access Control List (ACL), exploring its types, configuration, and implementation.What is a GHz Router Access Control List (ACL)?
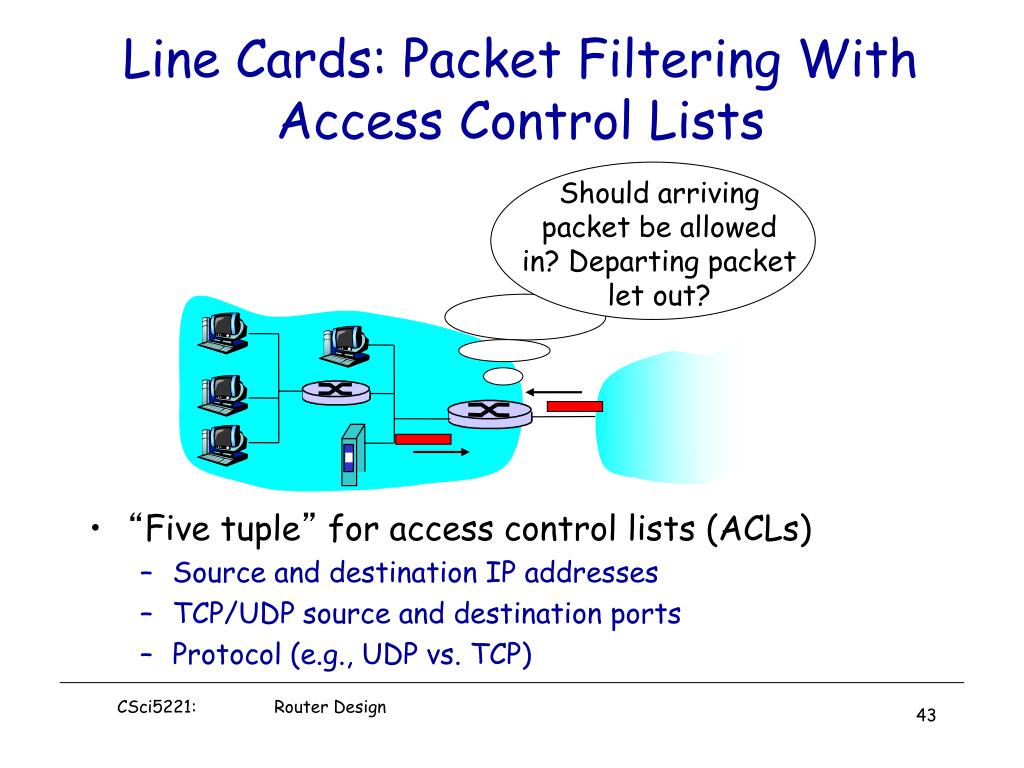
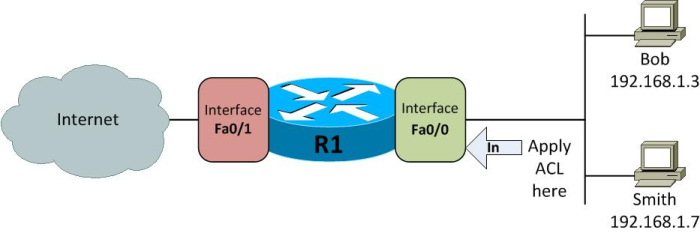
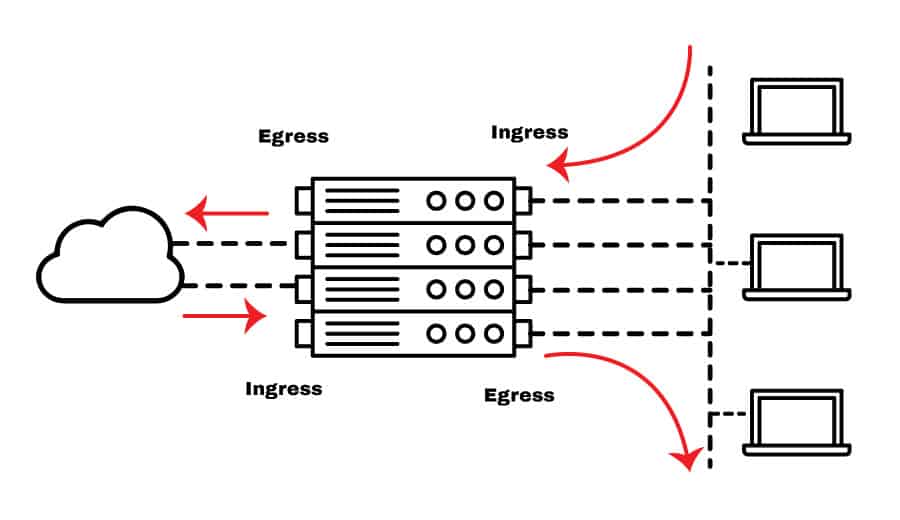
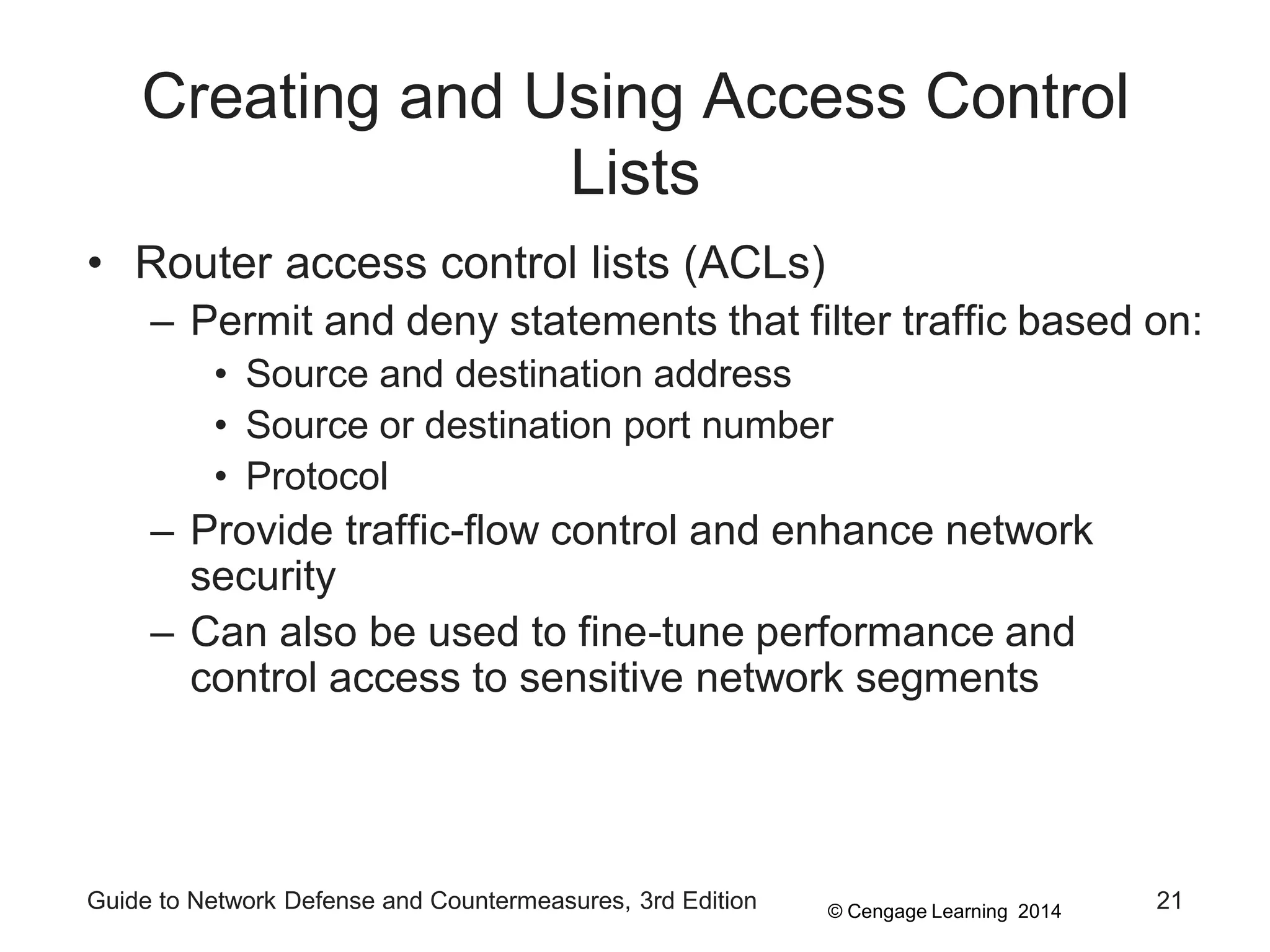
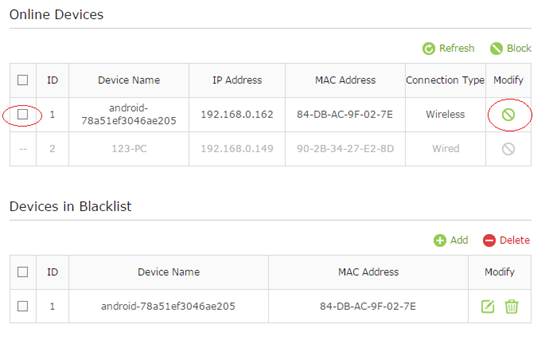
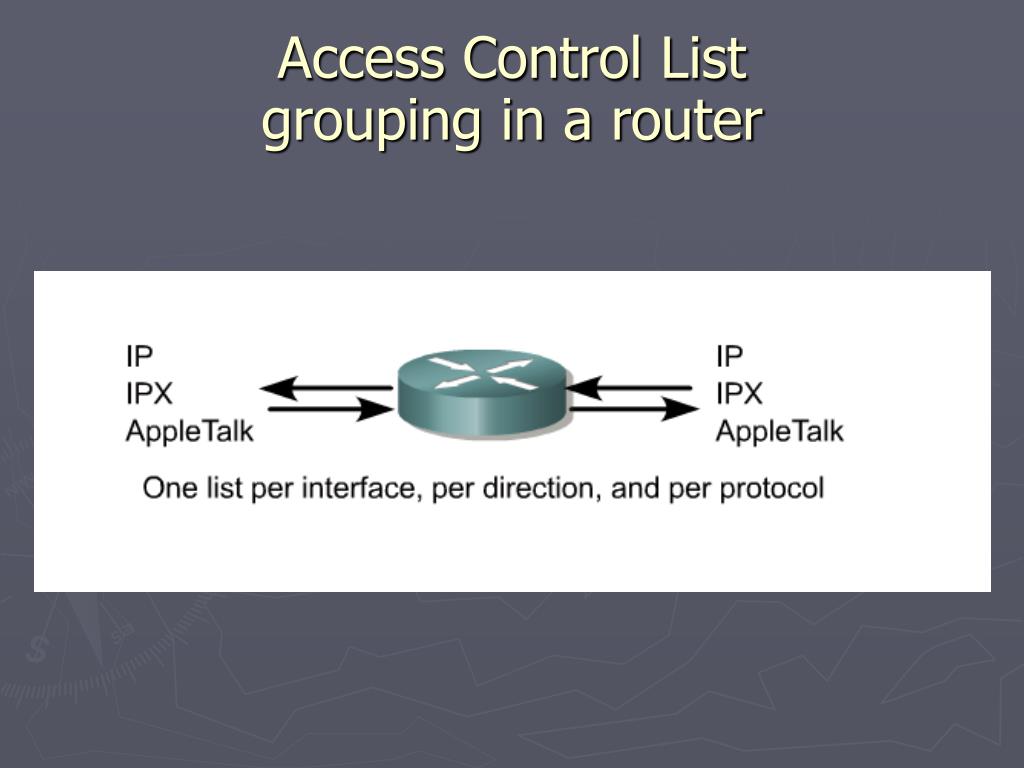
A GHz Router Access Control List (ACL) is a set of rules that control and filter network traffic based on source and destination IP addresses, port numbers, and protocols. These rules are applied to specific interfaces of a router, allowing or blocking packets from entering or exiting a network.Types of ACLs

Furthermore, visual representations like the one above help us fully grasp the concept of Ghz Router Access Control List.
There are two main types of ACLs: Standard and Extended.- Standard ACLs: Identified by numbers from 1 to 99 and 1300 to 1999, standard ACLs allow you to specify a source or destination IP address and a protocol. However, they do not allow you to specify port numbers or services.
- Extended ACLs: With numbers from 100 to 199 and 2000 to 2699, extended ACLs enable you to specify source and destination IP addresses, protocols, and services (such as HTTP or FTP).
How ACLs Work

Benefits of ACLs
The benefits of ACLs are numerous:- Enhanced security: By filtering network traffic, ACLs reduce the risk of spoofing and denial-of-service attacks.
- Improved performance: By controlling traffic, ACLs help optimize network performance.
- Increased control: ACLs allow administrators to grant or deny access to specific users, devices, or services.
Configuring ACLs
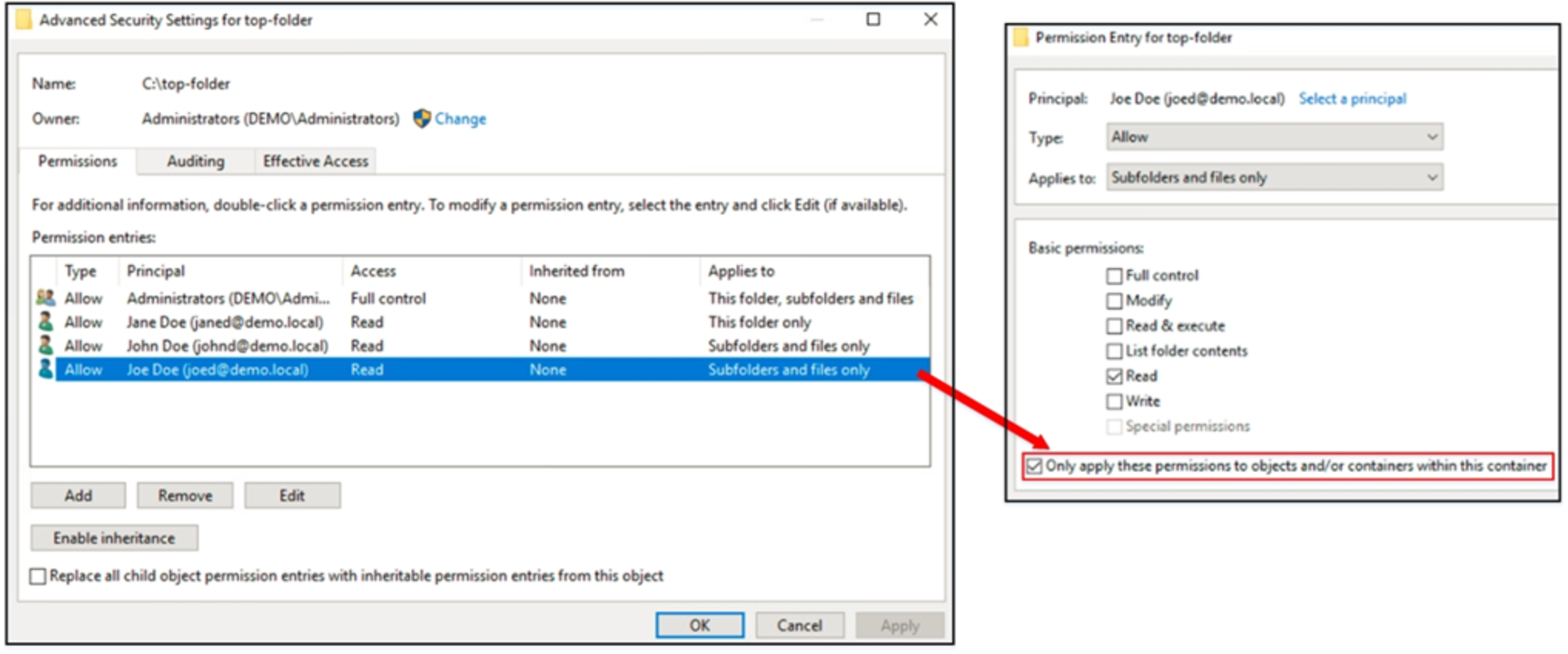
Configuring ACLs involves several steps: 1. Create an ACL: Define a set of rules to control network traffic. 2. Apply the ACL: Attach the ACL to a specific interface on the router. 3. Test and verify: Ensure the ACL is working as intended.Best Practices for Implementing ACLs
To maximize the effectiveness of ACLs, follow these best practices:- Use access lists at firewalls and routers.
- Define specific access lists for each network segment.
- Use explicit deny all at the end of each access list.








![Access Control Lists Overview and Guidelines [Support] View of Access Control Lists Overview and Guidelines [Support]](https://www.manageengine.com/network-configuration-manager/images/Putty_3.jpg)
![Access Control Lists: Overview and Guidelines [Support] Image showcasing Access Control Lists: Overview and Guidelines [Support]](https://image.slidesharecdn.com/nxld58securingswitchaccess-150429020249-conversion-gate01/85/Securing-Switch-Access-20-320.jpg)