Protecting WiFi Network from Vulnerability Exploitation
With the increasing reliance on wireless technology, protecting WiFi networks from vulnerability exploitation has become a vital component of modern cybersecurity. As wireless devices and networks proliferate in homes, businesses, and public spaces, ensuring robust WiFi security has become more important than ever.
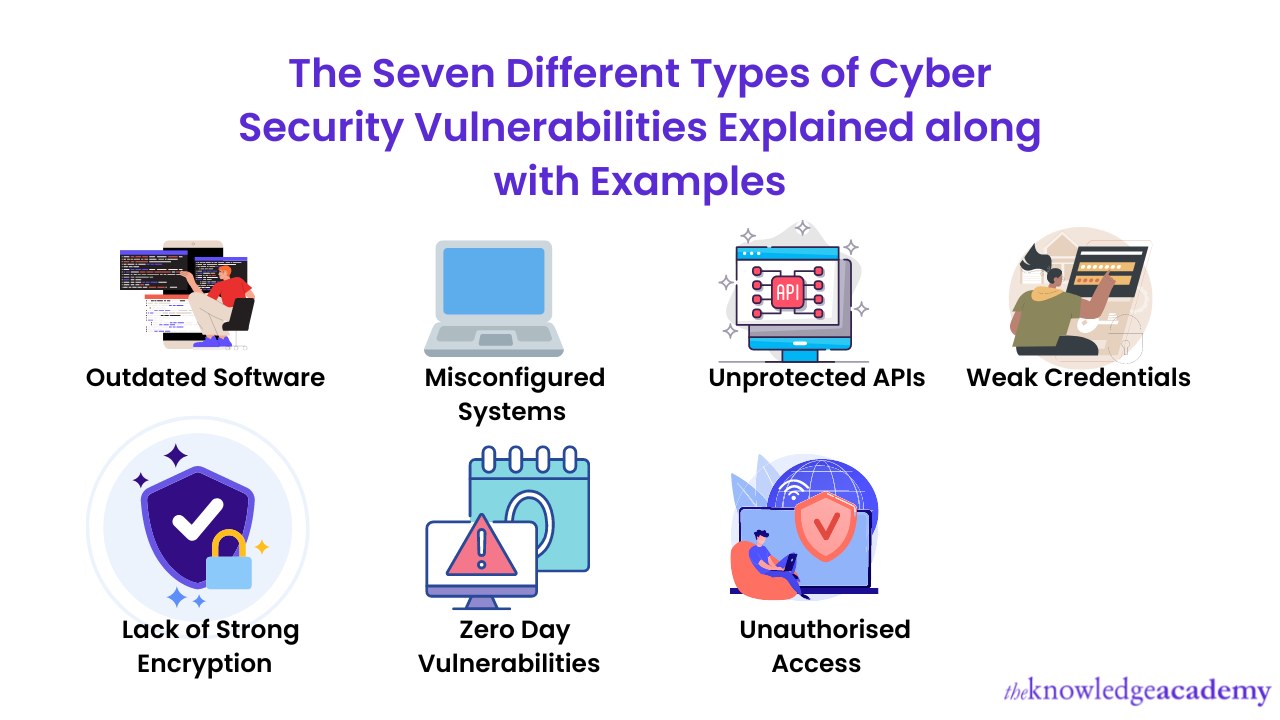
Understanding WiFi Network Vulnerabilities
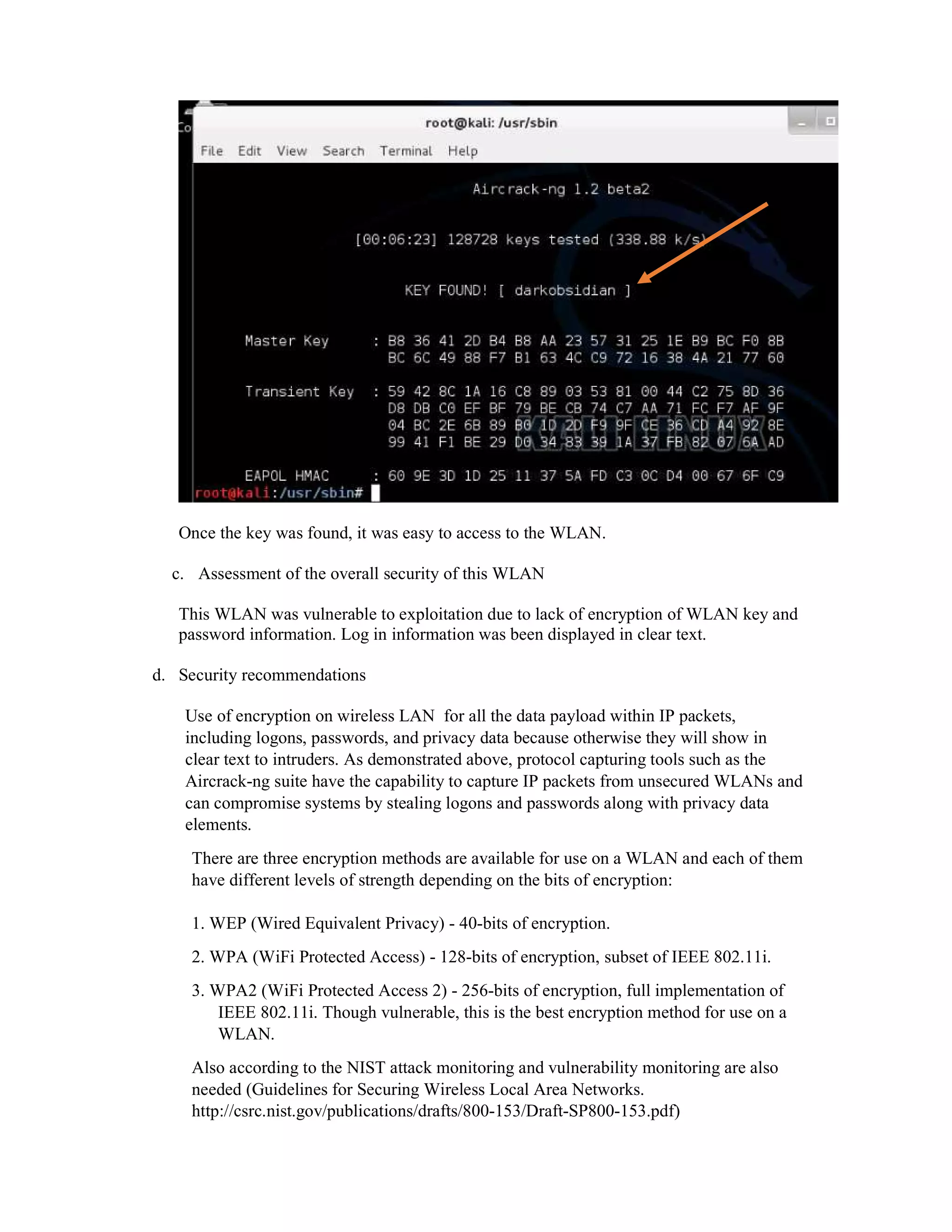
Wireless networks introduce additional security risks that traditional wired networks do not face. If you have a wireless network, it is essential to take appropriate precautions to protect your information from unauthorized access, eavesdropping, and other malicious activities.
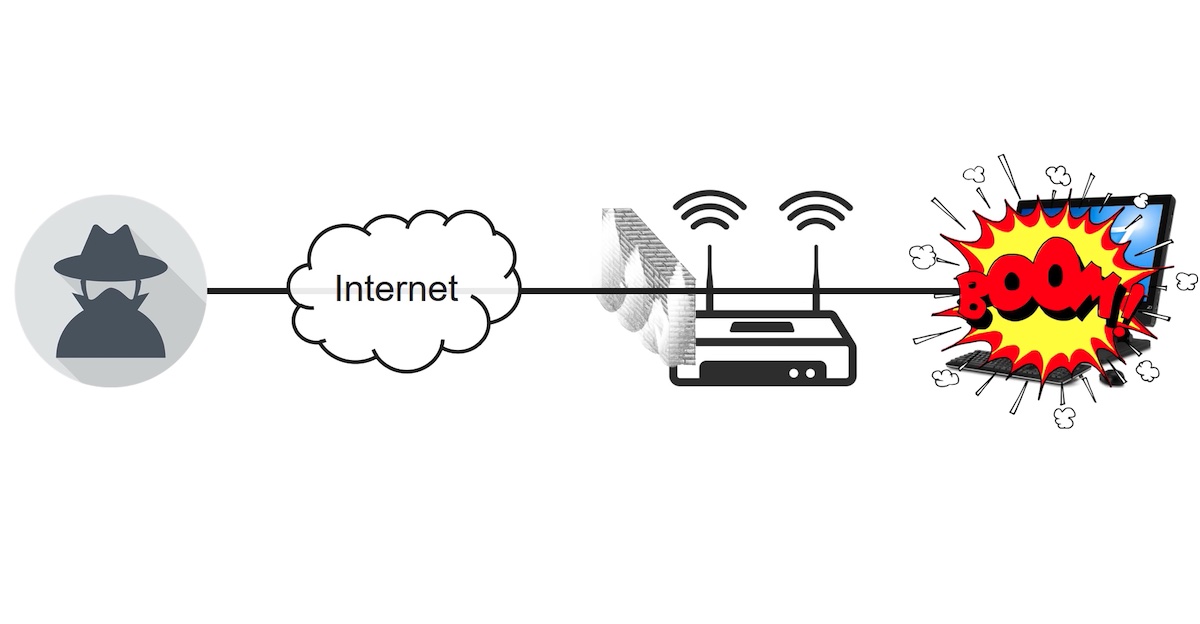
Securing WiFi networks means protecting against attacks such as Wi-Jacking, evil twin attacks, and bad KARMA. These attacks exploit vulnerabilities in wireless networks to compromise devices and steal sensitive information.
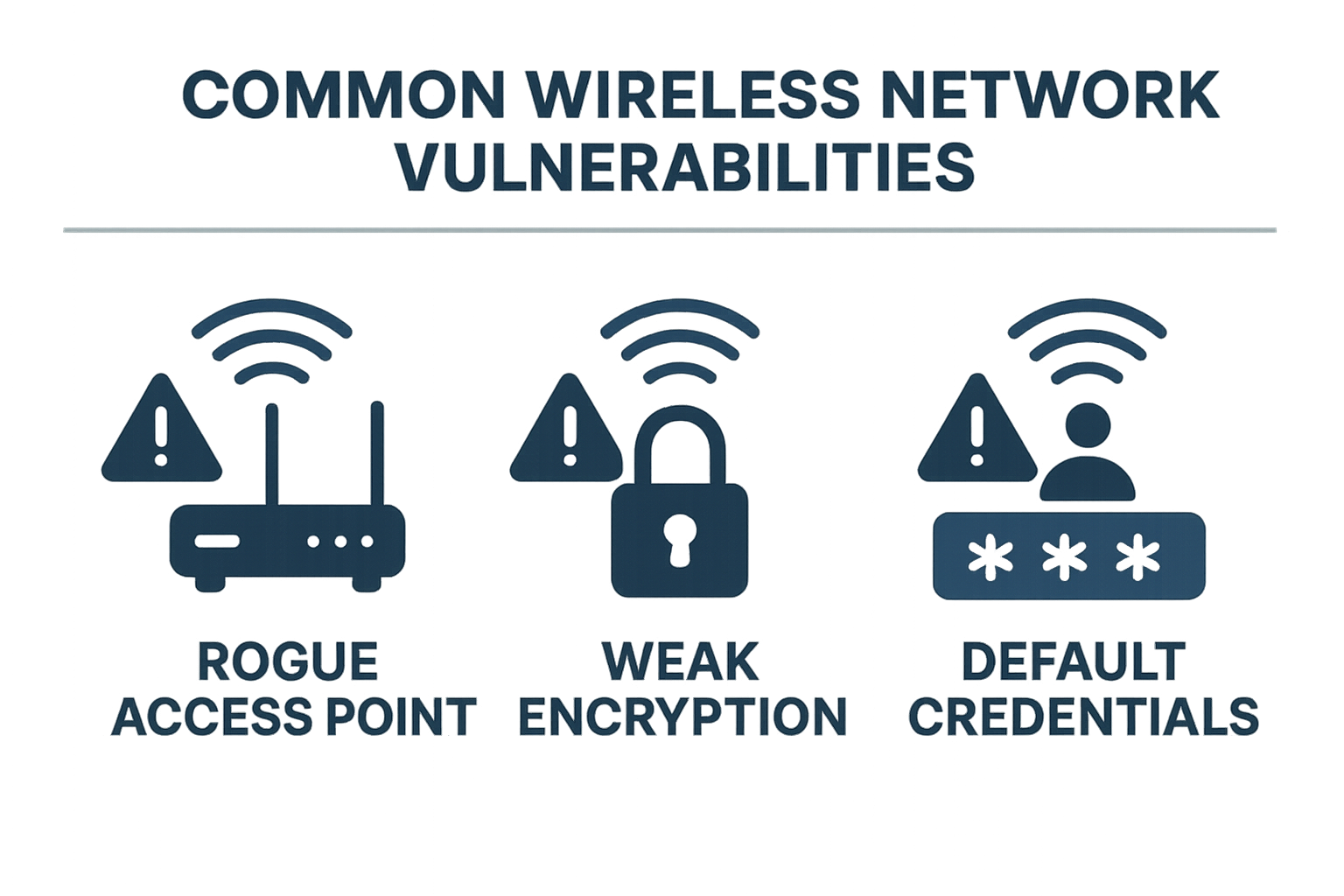
Common WiFi Network Vulnerabilities
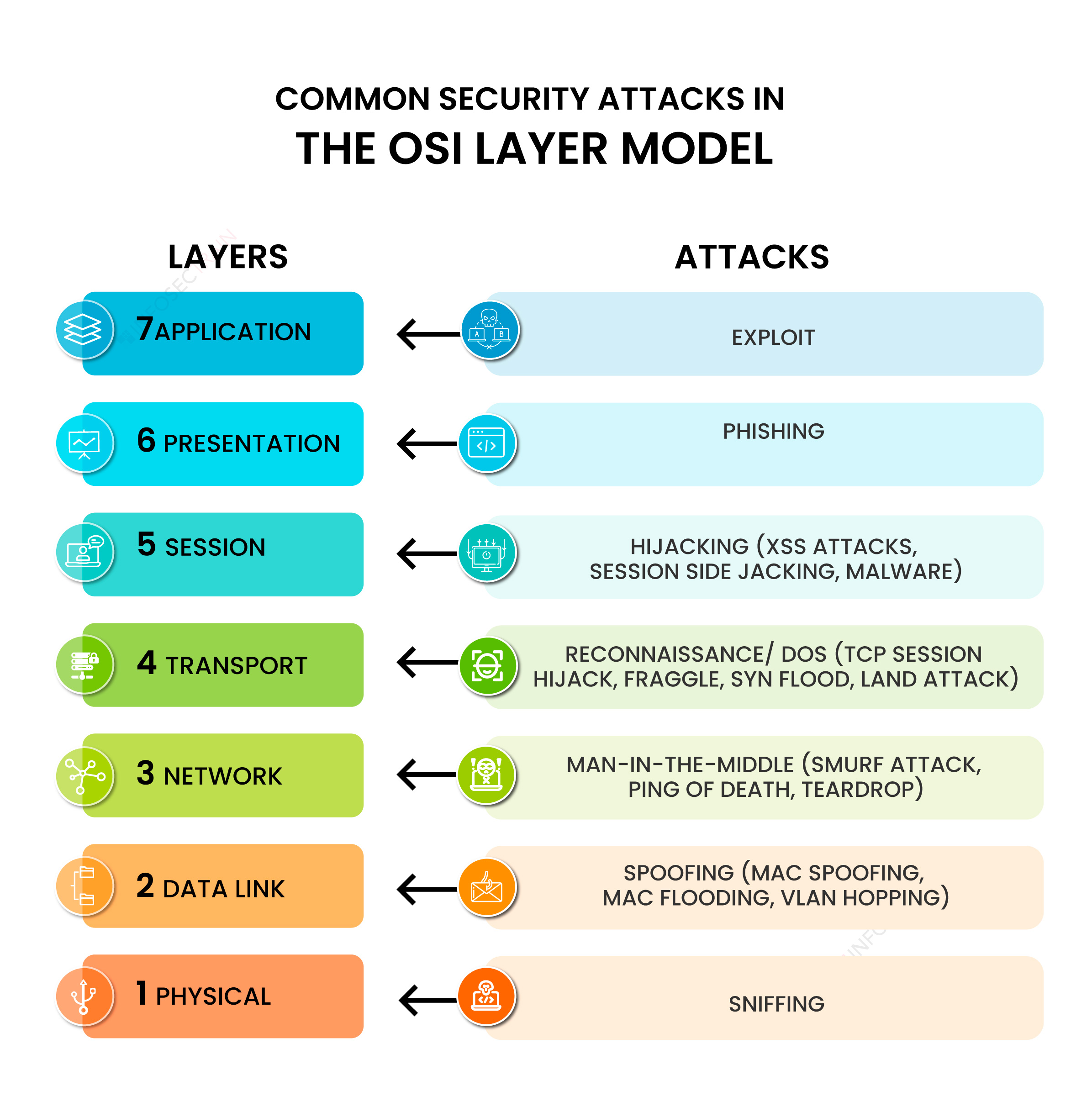
- Passive eavesdropping: Attackers use specialized equipment to listen to wireless network traffic, compromising sensitive information.
- Active attacks: Hackers inject malicious code or commands into encrypted WiFi traffic, compromising device security.
- Man-in-the-middle attacks: Attackers intercept and modify wireless network traffic, compromising device security and stealing sensitive information.
Preventing WiFi Network Hacks
To prevent WiFi network hacks, it is essential to implement robust security measures, including:

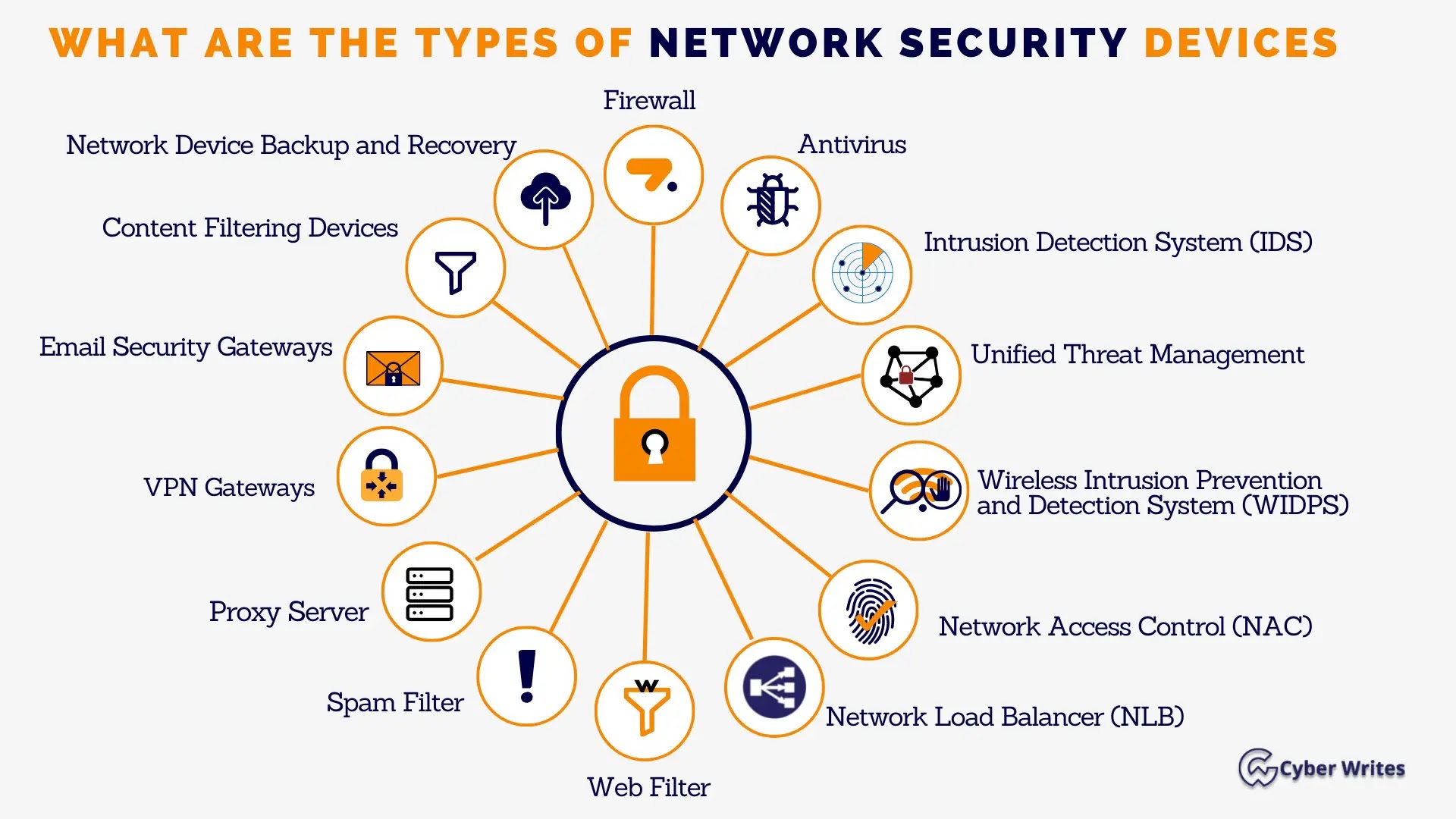
As we can see from the illustration, Protecting Wifi Network From Vulnerability Exploitation has many fascinating aspects to explore.
- Setting strong passwords and using WPA3 encryption
- Enabling 802.1X authentication and two-factor authentication
- Implementing a guest network for visitors
- Regularly updating and patching WiFi router firmware
- Using a VPN to encrypt WiFi traffic
- Monitoring network activity for suspicious behavior
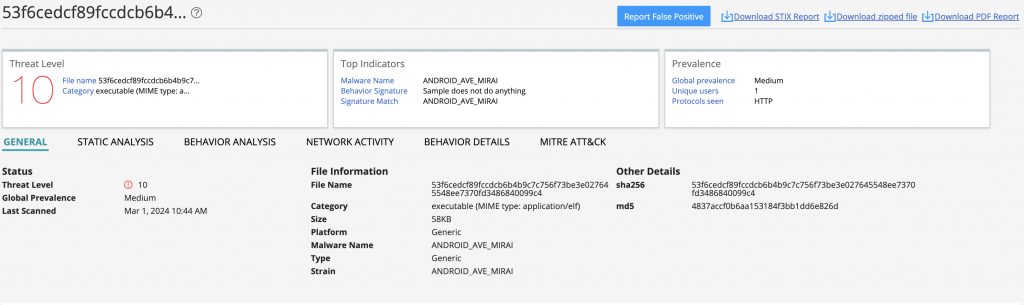
Enhanced Vulnerability Management
Enhanced vulnerability management is critical to protect against WiFi network exploitation. This involves:
Embracing OpenEoX, a collective community-driven initiative to proactively eliminate vulnerabilities and safeguard the digital ecosystem at scale.

Conclusion
Protecting WiFi networks from vulnerability exploitation requires a multi-layered approach that includes implementing robust security measures, monitoring network activity, and staying up-to-date with the latest security patches and updates.
References
For more information on protecting WiFi networks from vulnerability exploitation, refer to the following resources:
- Wi-Fi Security: Best Practices for Wireless Network Security
- The 10 Most Common WiFi Vulnerabilities and How to Fix Them
- Discovering Vulnerabilities in Home Routers: A Practical Experience
- Enhanced Vulnerability Management with OpenEoX
By staying informed and implementing effective security measures, you can protect your WiFi network from vulnerability exploitation and ensure a secure and reliable connection.













![Wi-Fi security: How to protect your wireless network [2026 guide] Image showcasing Wi-Fi security: How to protect your wireless network [2026 guide]](https://sekyour.com/images/2302/wireless-network-hacks-02-18-1.jpg)