Protect IP Address from Hackers: 7 Proven Methods to Safeguard Your Online Security
Understanding IP Address and Its Importance in Online Security
An IP address is a unique numerical label assigned to each device connected to a network that uses the Internet Protocol for communication. It serves two main purposes: identifying a device on the network and locating the device to enable communication with other devices over a network like the internet.
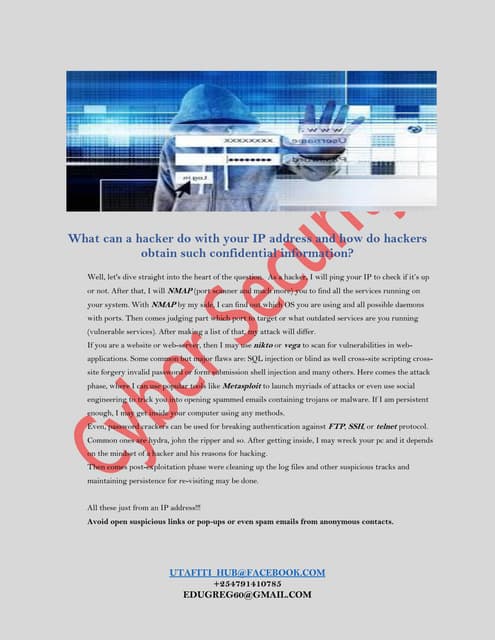
However, an IP address also poses a significant risk to online security. Hackers can use your IP address to scan for vulnerabilities, launch DDoS attacks, track your location, or access insecure IoT devices, potentially compromising your network or data. Therefore, it is essential to take steps to protect your IP address from hackers.
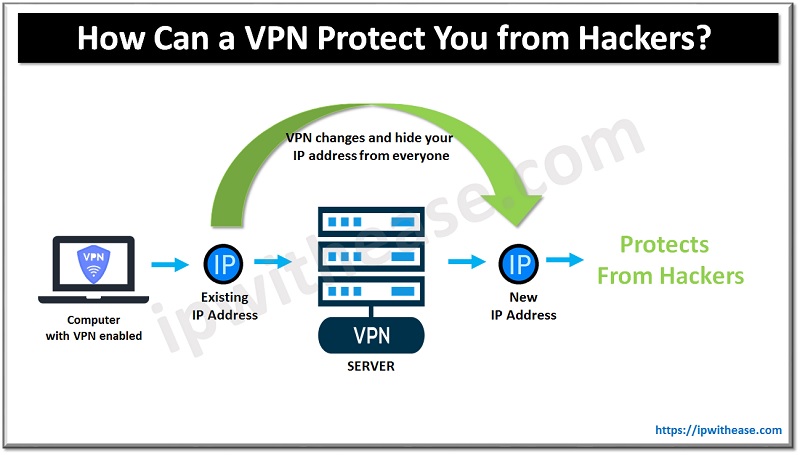
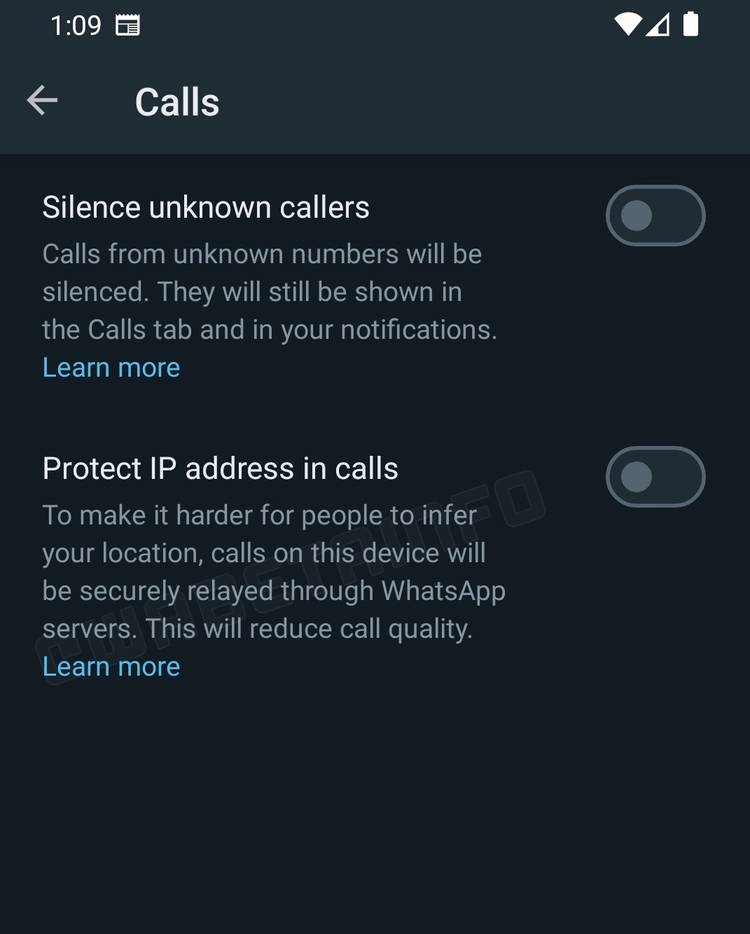
A VPN creates a secure and encrypted tunnel between your device and the internet, masking your IP address and personal data from hackers. By connecting to a VPN server, you can hide your IP address, location, and online activities from anyone who tries to monitor your internet traffic.
Method 2: Enable a Firewall
Enabling a firewall on your computer or network router acts as a barrier between your device and the internet, blocking unauthorized access to your IP address and personal data. Firewalls can detect and prevent potential threats, such as malware, Trojan horses, and hackers attempting to scan your network for vulnerabilities.
Method 3: Secure Your Router
Most routers come with a built-in firewall, which you should enable to block unauthorized access to your network and IP address. You should also disable any remote access features that may pose a security risk.
Method 4: Use Tor Browser
Tor Browser is a free, open-source web browser that anonymizes your internet traffic by routing it through multiple relays worldwide. This makes it difficult for hackers to track your IP address, location, and online activities.
By using Tor Browser, you can protect your IP address from hackers and maintain your online anonymity. However, keep in mind that Tor Browser may be slower than traditional browsers due to the routing process.
Method 5: Disable Any Unnecessary Network Services
Disabling any unnecessary network services reduces the attack surface of your network, making it harder for hackers to find vulnerabilities and exploit them.
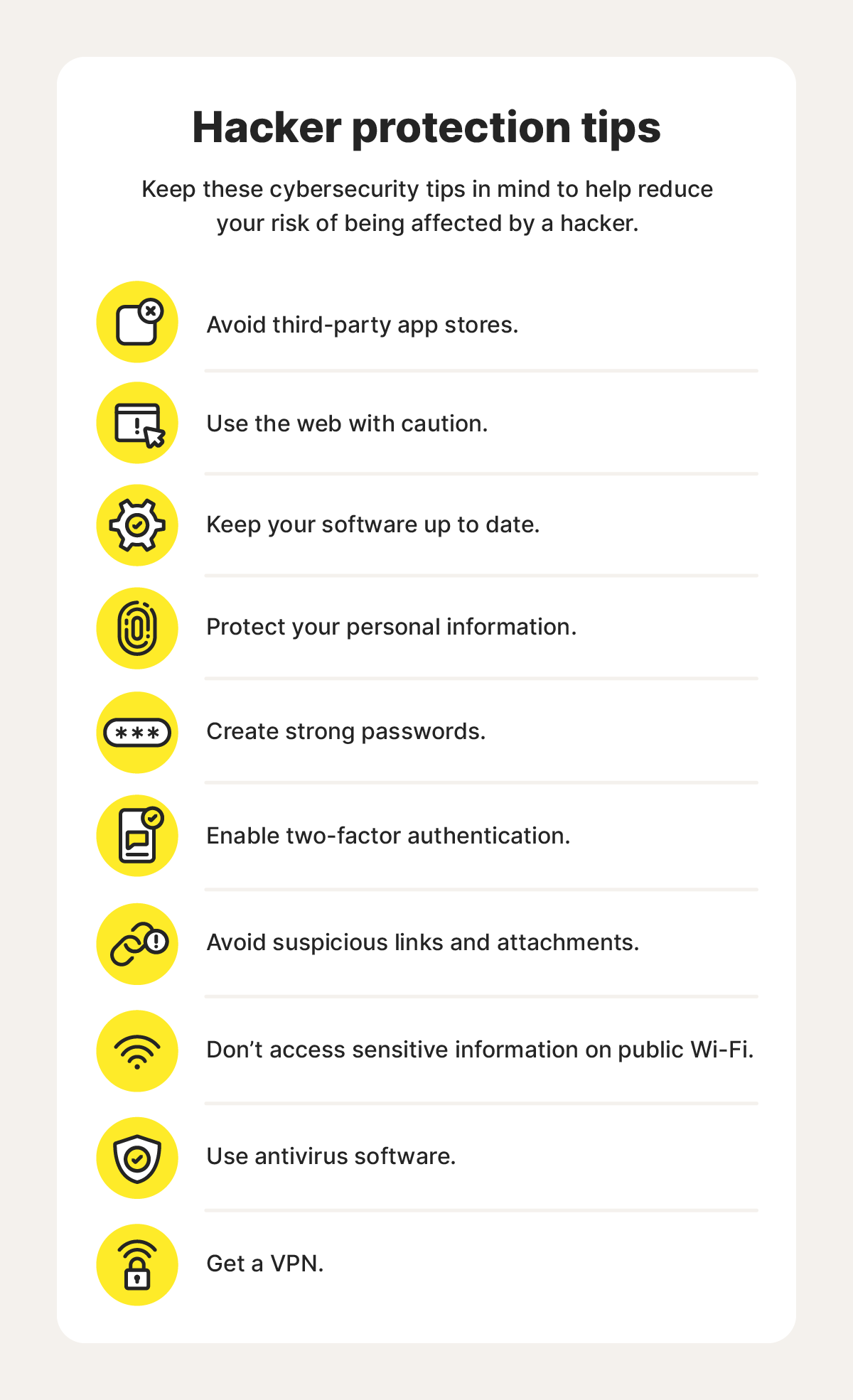
Regularly updating your operating system and software ensures that any known vulnerabilities are patched, reducing the risk of unauthorized access to your IP address and personal data.
Set your operating system and software to install updates automatically, and enable the auto-update feature to ensure your device stays secure and protected from hackers.
As we can see from the illustration, Protect Ip Address From Hackers has many fascinating aspects to explore.
Method 7: Monitor Your Network Traffic
Monitoring your network traffic helps you identify any potential security threats and take corrective action to protect your IP address from hackers.
Use network monitoring tools to detect and respond to any security incidents, and ensure you have a clear understanding of your network traffic to prevent unauthorized access to your IP address and personal data.
Protecting your IP address from hackers requires a combination of good security practices and using appropriate tools. By implementing the 7 methods outlined in this article, you can safeguard your online security, maintain your anonymity, and prevent unauthorized access to your IP address and personal data.
- VPN Mentor - A comprehensive guide to VPNs and their benefits in protecting your IP address from hackers.
- Firewall CX - A network security resource that provides tutorials, guides, and advice on firewalls and network security.
- Tor Project - A non-profit organization that develops the Tor Browser and promotes online anonymity and security.
Protecting your IP address from hackers is a critical concern in today's digital age. By implementing the 7 methods outlined in this article, you can safeguard your online security, maintain your anonymity, and prevent unauthorized access to your IP address and personal data.