How to Protect Identity from Phishing: A Comprehensive Guide
Phishing is a type of cybercrime that involves tricking individuals into revealing sensitive information, such as passwords, credit card numbers, or personal identification numbers. In this article, we will discuss the ways in which individuals can protect their identity from phishing attacks.
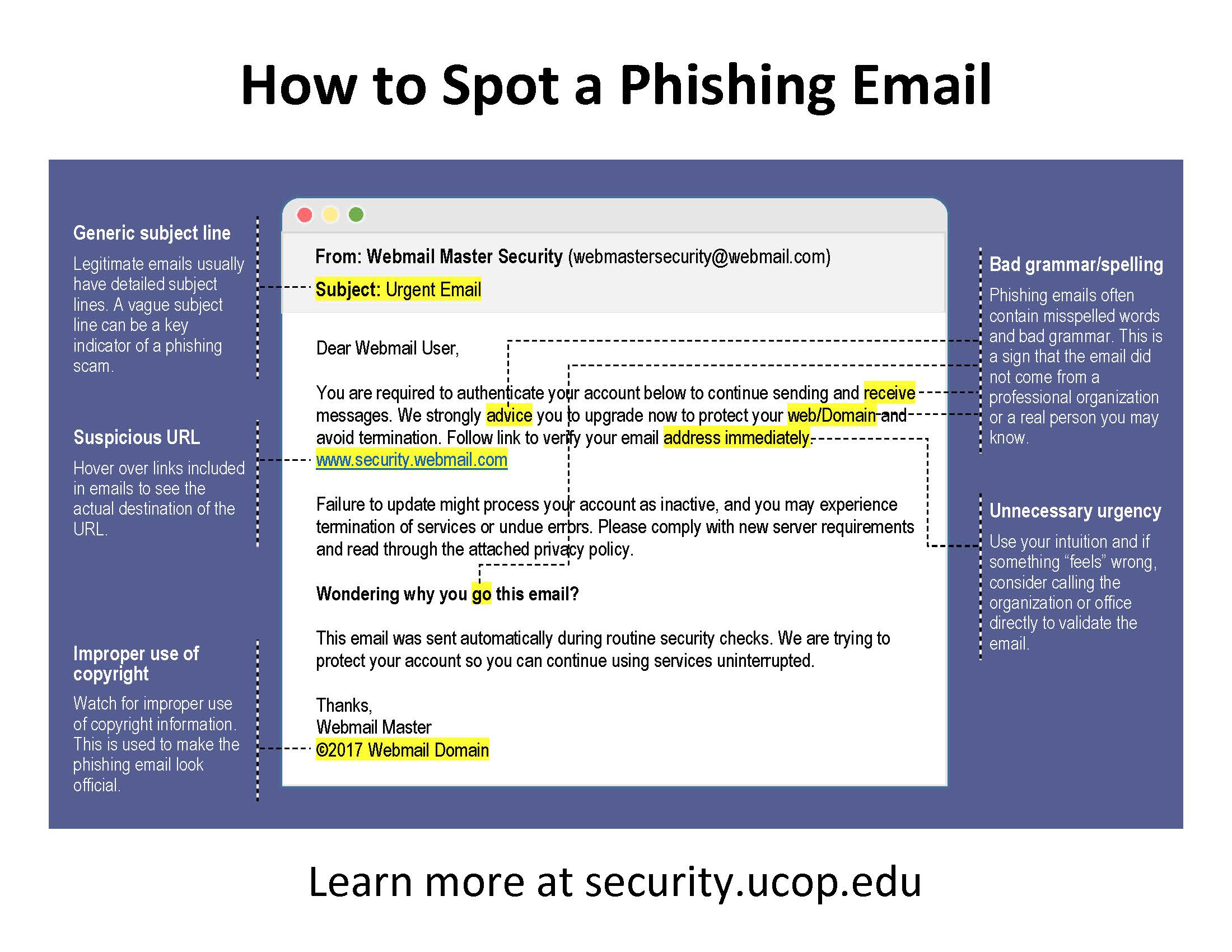
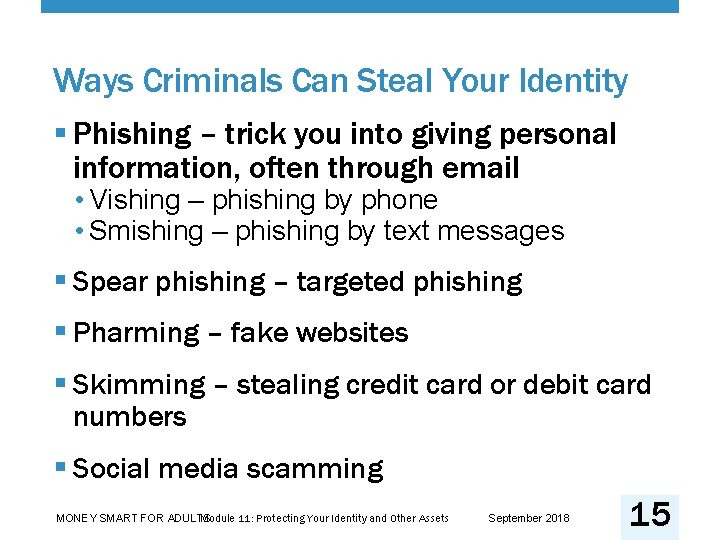
Phishing is a type of social engineering attack that involves using various tactics to trick individuals into revealing sensitive information. This can be done through emails, phone calls, text messages, or even in-person interactions. The goal of phishing is to gain unauthorized access to a person's data, which can be used for financial gain or other malicious purposes.
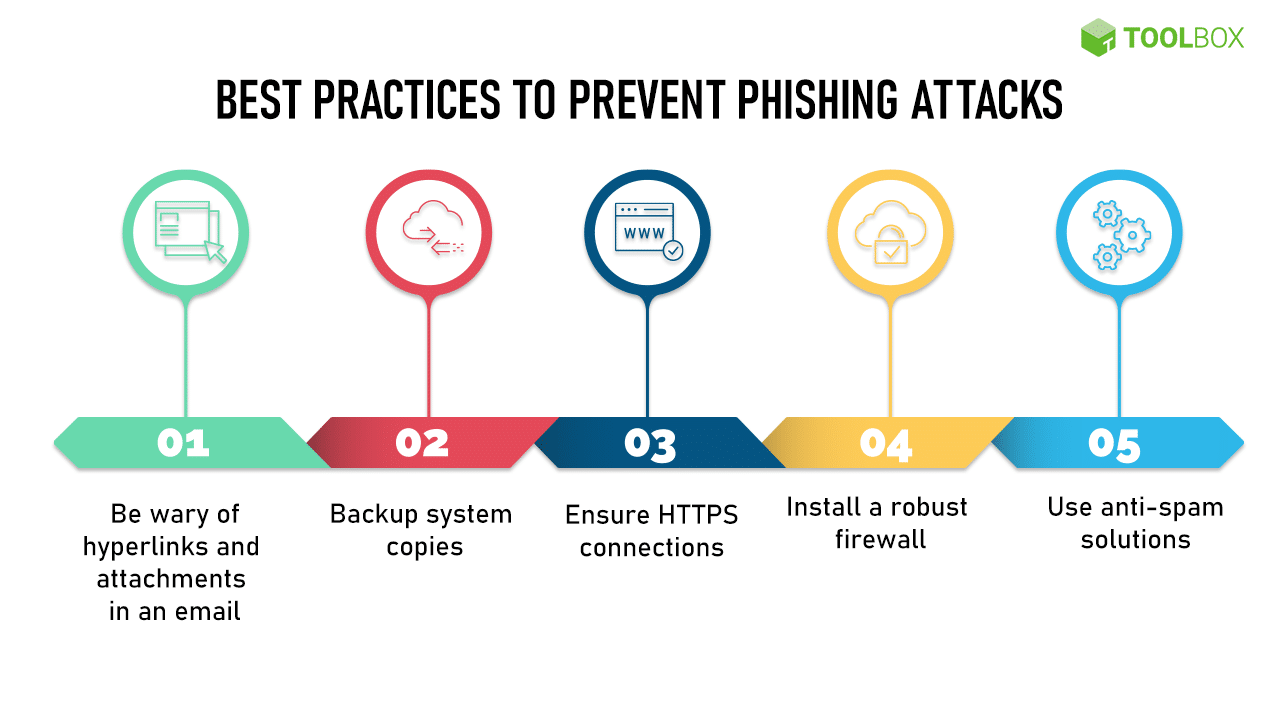
Four Ways to Protect Yourself from Phishing
Protecting yourself from phishing attacks requires a combination of knowledge, awareness, and active measures. Here are four ways to protect yourself from phishing attacks:
- Protect your computer by using security software. Set the software to update automatically so it will deal with any new security threats.
- Protect your cell phone by setting software to update automatically. This will ensure that your phone has the latest security patches and threats are identified and dealt with.
- Be cautious when clicking on links or downloading attachments from unknown sources. Verify the authenticity of the sender and the content of the message before taking any action.
- Use strong and unique passwords for all of your online accounts. Consider using a password manager to generate and store complex passwords securely.

Such details provide a deeper understanding and appreciation for How To Protect Identity From Phishing.
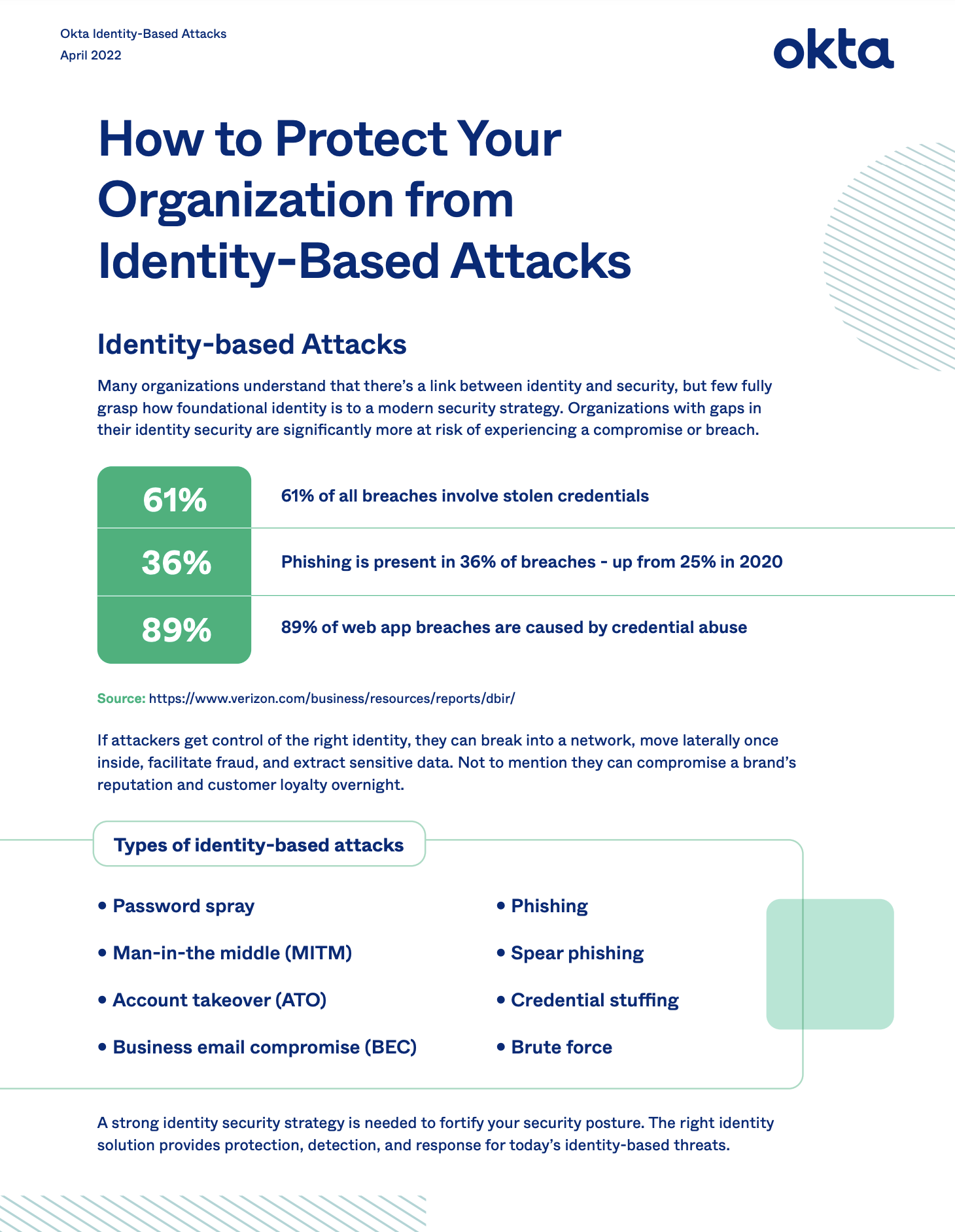
How Phishing Works
Phishing attacks typically involve a combination of tactics to trick individuals into revealing sensitive information. These tactics can include:
- Spam emails: Phishers send out large quantities of spam emails that appear to be from legitimate sources, such as banks or financial institutions.
- Phishing websites: Phishers create websites that appear to be legitimate, but are actually designed to steal sensitive information. li>Text messages: Phishers send text messages that appear to be from legitimate sources, but are actually designed to steal sensitive information.
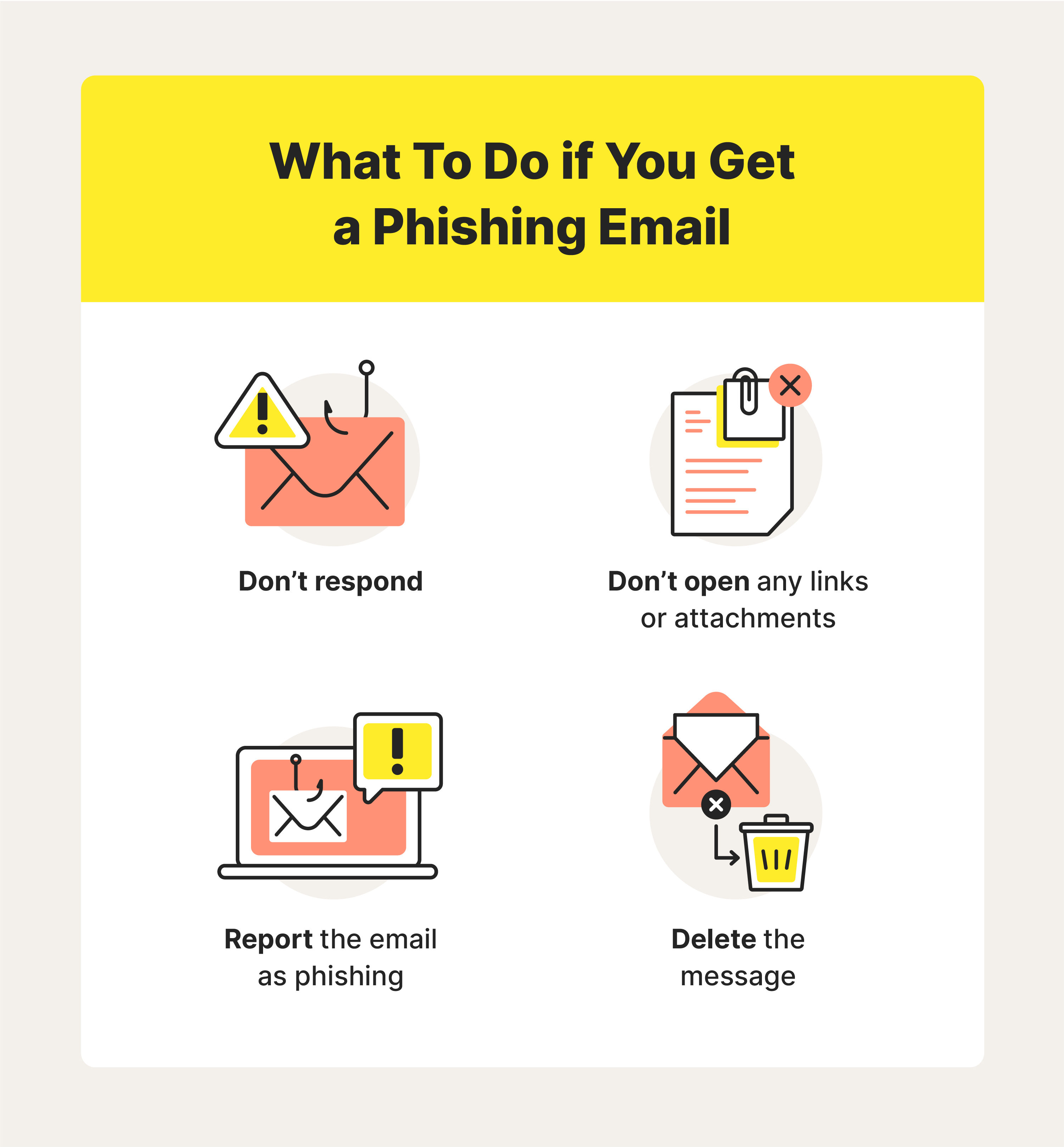
What to Do if You Fall Victim to Phishing
If you fall victim to a phishing attack, it is essential to take immediate action to minimize the damage. Here are some steps to take:

- Change all of your passwords, including your bank and credit card passwords.
- Monitor your accounts for any suspicious activity.
- Report the incident to the relevant authorities, such as the Federal Trade Commission.
- Consider setting up identity theft protection services to monitor your credit report and detect any potential identity theft.
Tips to Fight Identity Theft
Identity theft is a serious crime that can have long-lasting consequences. Here are some tips to fight identity theft:
Conclusion
Phishing is a serious cybercrime that can have devastating consequences. By being aware of the tactics used by phishers and taking proactive measures to protect yourself, you can minimize the risk of falling victim to a phishing attack. Remember to protect your computer and phone, be cautious when clicking on links or downloading attachments, and use strong and unique passwords for all of your online accounts. If you do fall victim to a phishing attack, take immediate action to minimize the damage and report the incident to the relevant authorities.