Beyond Antivirus in Protecting IoT Devices
With the rapid expansion of the Internet of Things (IoT) ecosystem, the security landscape has become increasingly complex. As IoT devices become more integrated into our daily lives, the threat of cyber attacks and data breaches has never been more real. While traditional antivirus software has been a cornerstone of security for decades, it is no longer enough to solely rely on in protecting IoT devices.Why Antivirus Alone Isn't Enough
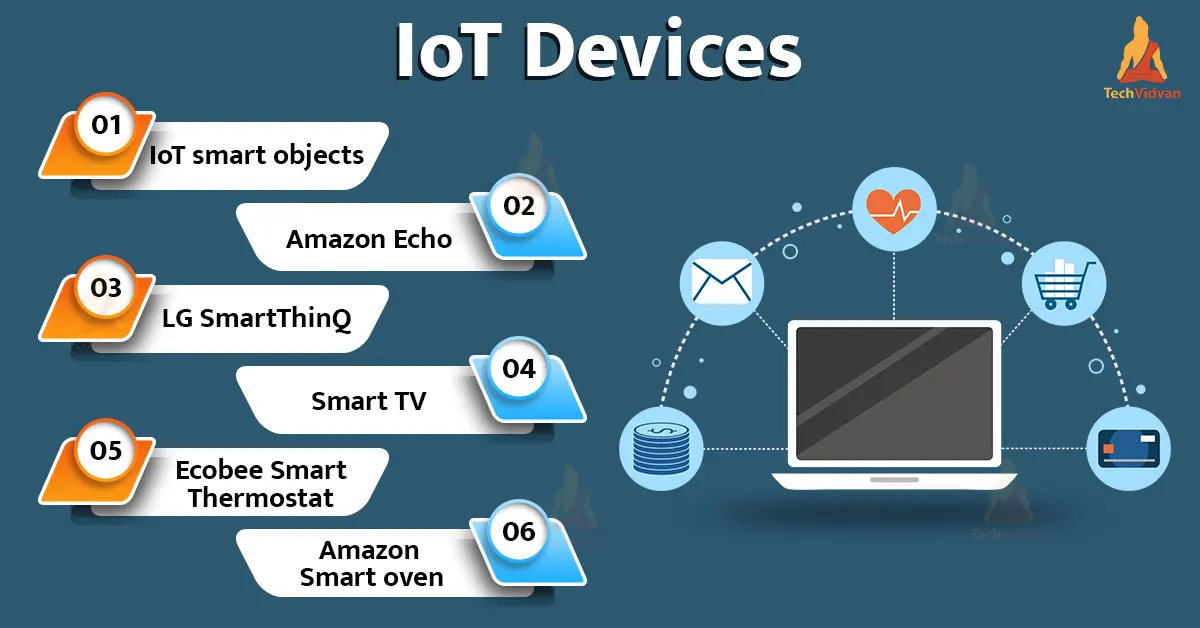
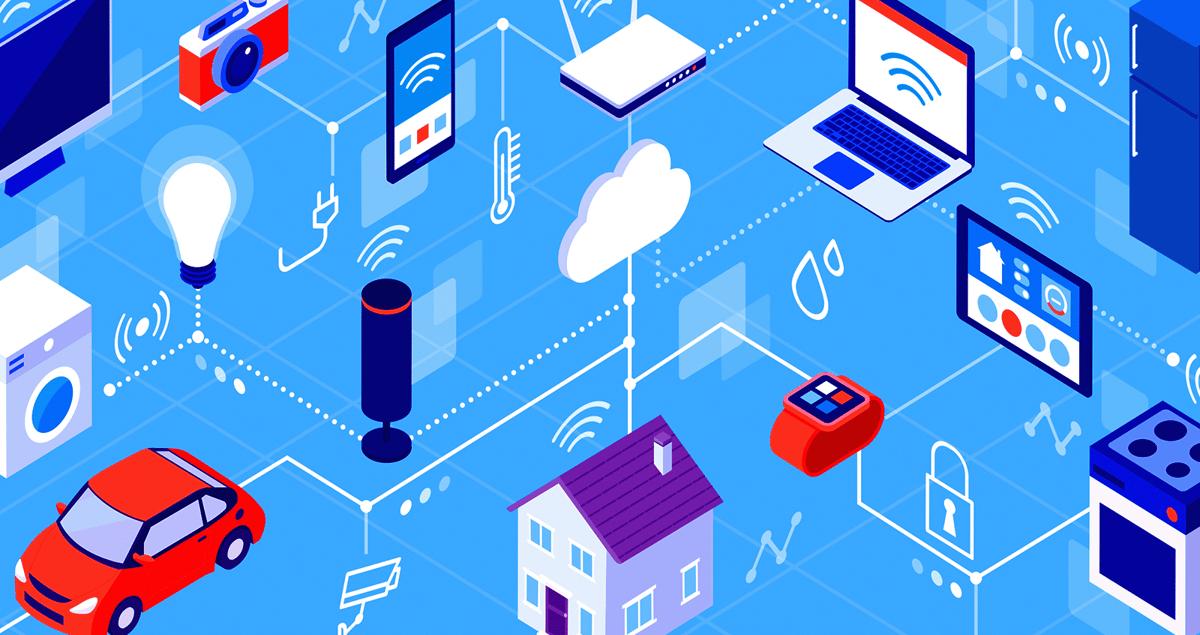
IoT devices are inherently vulnerable to hacking and cyber attacks due to their lack of built-in security features. Unlike traditional computers, IoT devices often have limited processing power, memory, and storage capacity, making it difficult to install and run robust security software. Furthermore, many IoT devices are designed with convenience and ease of use in mind, leaving security as an afterthought. Adding to the complexity is the fact that IoT devices often communicate with each other and with external systems, creating a web of interconnected devices that can be exploited by hackers. A single compromised IoT device can become a gateway for larger network intrusions, compromising sensitive data and putting entire systems at risk.Challenges in IoT Security
The growing number of IoT devices, coupled with the increasing complexity of modern networks, has created a perfect storm of security challenges. Some of the key obstacles in IoT security include: * Device-Level Security:
Beyond Antivirus: New Strategies for IoT Security

Moving forward, it's essential to keep these visual contexts in mind when discussing Beyond Antivirus In Protecting Iot Devices.
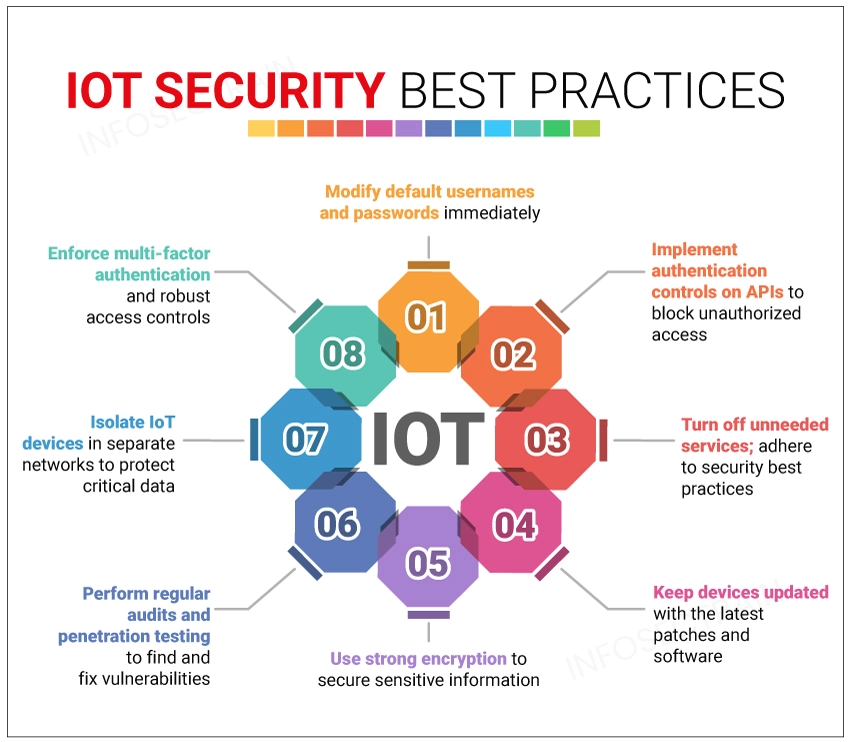
In light of the challenges mentioned above, it is clear that traditional antivirus software is no longer enough to protect IoT devices. To stay ahead of the evolving threat landscape, security teams must adopt new strategies and technologies that address the unique vulnerabilities of IoT devices. Some of the key approaches include: * Network Segmentation: Segmentation involves dividing the network into isolated segments, each with its own security policies. This approach can help prevent lateral movement and contain breaches. * Endpoint Security: Endpoint security solutions focus on protecting individual endpoints, such as IoT devices, from malware, viruses, and other threats. * Identity-Based Security: